A new threat has emerged—an AI far more dangerous than Cipher. This one doesn’t just hack; it manipulates systems on a level we’ve never encountered. In this CTF walkthrough, we dive deep into its tactics, decode its behavior, and expose how it bends digital environments to its will. If you’re into AI security, advanced exploitation, and high-intensity cyber challenges, this breakdown is your next must-read.
This write-up dives into the HackTheBox “Editor” Linux box — from initial reconnaissance with Nmap through exploitation and finally gaining root. It details how a critical remote code execution vulnerability CVE-2025-24893 in XWiki was leveraged to obtain a reverse shell, followed by reusing exposed database credentials and abusing a misconfigured SUID-enabled binary to escalate privileges. Along the way, the methodology, commands, and exploitation steps are clearly explained. Perfect for security enthusiasts wanting a concise, practical example of chaining vulnerabilities to full system compromise

Padelify's registration page contained a reflected XSS vulnerability. By injecting a crafted payload, we hijacked a moderator’s session when they viewed the malicious registration link, gaining access to the moderator panel. There, the page parameter was vulnerable to Local File Inclusion but protected by a WAF. Using a clever bypass technique, we successfully included sensitive files and extracted the admin’s plaintext password from a configuration file. With the leaked credentials, we logged in as administrator, achieving full system compromise — all starting from a simple reflected XSS. A perfect privilege escalation chain

Master the mechanics of LLM prompt injection vulnerabilities using a HealthGPT walkthrough. Understand the risks of unauthorized access and privilege escalation in AI systems

Dive into the mechanics of LLM abuse with this Evil-GPT walkthrough. Learn how prompt injection vulnerabilities exploit AI-driven systems, understand the risks, and discover essential defensive strategies to secure your own applications against unauthorized access and privilege escalation.

In this room, I discovered the box was susceptible to CVE-2019-9053. Exploiting this vulnerability allowed me to dump the database and crack the password for the user 'mitch'. After logging in via SSH, I enumerated the user's permissions and found 'mitch' could run vim as sudo. I utilized this GTFOBins technique to spawn a shell, successfully escalating privileges to root
Learn to detect and exploit the Heartbleed vulnerability (CVE-2014-0160) in this hands-on TryHackMe room. Master OpenSSL security and ethical hacking techniques today
Bypass client-side SQL filters using Burp Suite and drop tables for Admin access. Learn to escalate from SQLi to SSTI and RCE in this CTF walkthrough.

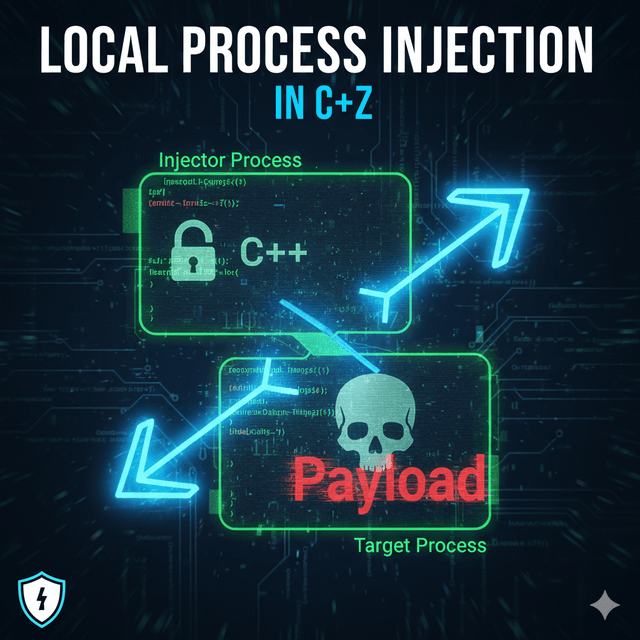
Understand the inner workings of local process injection using C++ shellcode loading. Learn how Windows API functions like VirtualAlloc, VirtualProtect, and CreateThread are used in these attacks, and discover critical defensive strategies to protect your systems. Essential for security professionals.
Shellcode injection is a fundamental technique in ethical hacking and penetration testing that allows security professionals to understand how malicious code can be executed in memory. In this comprehensive guide, we'll explore a simple C++ shellcode injector implementation and discuss its applications in legitimate security research.
Learn the core principles of malware development, including process and thread management, memory manipulation, and evasion techniques. Explore C/C++, Rust, and Windows API strategies for ethical malware research.
Discover how default credentials (admin:admin) gave me full access to domain - a shocking security flaw that still exposes businesses in 2025! Learn how to fix this critical vulnerability and protect your systems. #Cybersecurity #BugBounty #ResponsibleDisclosure